First of guys let me tell you its virtually impossible to see the actual
data that is transferring during a transaction but using session
hijacking and packet sniffing we can achieve that but that also is in
the encrypted format so if we are able to get that then we can move to
further step to crack the encrypted data. So lets start the tutorial...
What really is attack?
The fatal flaw that enabled the sensitive information to be stolen is
possible when an end-user is not properly educated on an easy to do and
well-known SSL exploit – SSL MITM. The hackers take benefit of that to
get access your sensitive data. As its a great saying PREVENTION IS
BETTER THAN CURE. So an properly educated end user is really the
requirement so that he can block all loopholes in the system. I have
already shared two articles with you about how to secure yourself. First
one is Make your computer 100% hacker proof (Click here to read) and other is 10 easy tips to secure your computer(click here to read) .
How the Hack works and How to do it?
First thing i will tell you hacking credit or debit cards is illegal and
it will result in serious consequences like 10 years imprisonment and
much more. This tutorial is for educational purposes only. I am
explaining this tutorial is just to make you aware that how it works.
How the hacker will do it?? suppose you are using a wifi connection to
connect to internet. Now what hacker will do it will hack your wifi
network ( to learn how to hack wifi click here)
and connect to it. He runs a series of utilities to redirect other
user’s data through his machine. He runs a number of other utilities to
sniff the data, act as an SSL Certificate Server and to be the
Man-the-Middle.
The following diagram shows a very simplified graphic of how your SSL
Banking session should work under normal conditions, then how it would
work during an attack:
An important concept to grasp here is that a certificate is used to
establish the secure SSL connection. This is a good thing, if you have a
good certificate and are connecting directly to the website to which
you intended to use. Then all your data is encrypted from your browser
to the SSL website where the bank’s website will use the information
from the certificate it gave you to decrypt your data/credentials. If
that istruly the
case, then it is pretty darn hard for a hacker to decrypt the
data/credentials being transmitted, even if he is able to sniff your
data.
This is a bad thing if you have a “Fake” certificate being sent from the
hacker, and you are actually connecting to his machine, not directly to
the bank’s website. In this case, your credentials are being
transmitted between your browser and the hacker’s machine. The hacker is
able to grab that traffic, and, because he gave you the certificate to
encrypt the data/credentials, he can use that same certificate to
decrypt your data/credentials.
EXACT STEPS TO HACK CREDIT CARDS OR DEBIT CARDS
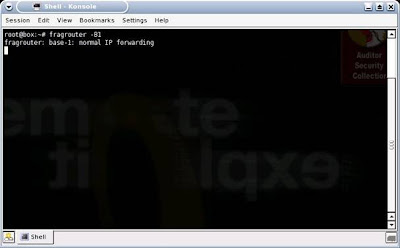
The first thing he would do is turn on Fragrouter, so that his machine can perform IP forwarding
After that, he’ll want to direct your Wi-Fi network traffic to his
machine instead of your data traffic going directly to the
Internet. This enables him to be the “Man-in-the-Middle” between your
machine and the Internet. Using Arpspoof,
a real easy way to do this, he determines your IP address is
192.168.1.15 and the Default Gateway of the Wi-Fi network is
192.168.1.1:
The next step is to enable DNS Spoofing via DNSSpoof:
Since he will be replacing the Bank's or Online Store’s valid
certificate with his own fake one, he will need to turn on the utility
to enable his system to be the Man-in-the-Middle for web sessions and to
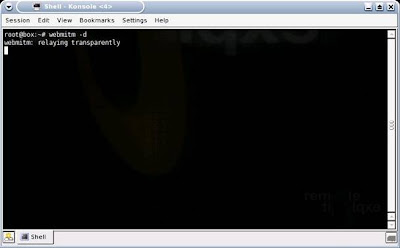
handle certificates. This is done via webmitm:
At this point, he is setup and ready to go, he now needs to begin
actively sniffing your data passing through his machine including your
login information and credit card info. He opts to do this with Ethereal, then saves his capture:
He now has the data, but it is still encrypted with 128-bit SSL. No
problem, since he has the key. What he simply needs to do now is decrypt
the data using the certificate that he gave you. He does this with SSL Dump:
The data is now decrypted and he runs a Cat command to view the now
decrypted SSL information. Note that the username is “Bankusername” and
the password is “BankPassword”. Conveniently, this dump also shows that
the Banking site as National City. FYI, the better, more secure banking
and online store websites will have you first connect to another,
preceeding page via SSL, prior to connecting to the page where you enter
the sensitive information such as bank login credentials or credit card
numbers. The reason for this is to stop the MITM-type attack. How this
helps is that if you were to access this preceeding page first with a
"fake" certificate and then proceeded to the next page where you were to
enter the sensitve information, that page where you would enter the
sensitive information would not display. That is because the page
gathering the sensitive information would be expecting a valid
certificate, which it would not receive because of the
Man-in-the-Middle. While some online banks and stores do implement this
extra step/page for security reasons, the real flaw in this attack is
the uneducated end-user, as you'll soon see:
With this information, he can now log into your Online Banking Account
with the same access and privileges as you. He could transfer money,
view account data, etc.
Below is an example of a sniffed SSL credit card purchase/transaction.
You can see that Elvis Presley was attempting to make a purchase with
his credit card 5440123412341234 with an expiration date of 5/06 and the
billing address of Graceland in Memphis, TN (He is alive!). If this was
your information, the hacker could easily make online purchases with
your card.
Also Real Bad News for SSL VPN Admins
This type of attack could be particularly bad for corporations. The
reason for this is that Corporate SSL VPN solutions are also vulnerable
to this type of attack. Corporate SSL VPN solutions will often
authenticate against Active Directory, the NT Domain, LDAP or some other
centralized credentials data store. Sniffing the SSL VPN login then
gives an attacker valid credentials to the corporate network and other
systems.
What an End-User Needs To Know
There’s a big step and end-user can take to prevent this from taking
place. When the MITM Hacker uses the “bad” certificate instead of the
“good”, valid certificate, the end-user is actually alerted to this. The
problem is that most end-users don’t understand what this means and
will unknowingly agree to use the fake certificate. Below is an example
of the Security Alert an end-user would receive. Most uneducated
end-users would simply click “Yes”… and this is the fatal flaw:
By clicking “Yes”, they have set themselves up to be hacked. By clicking
the “View Certificate” button, the end-user would easily see that there
is a problem. Below are examples of the various certificate views/tabs
that show a good certificate compared to the bad certificate:
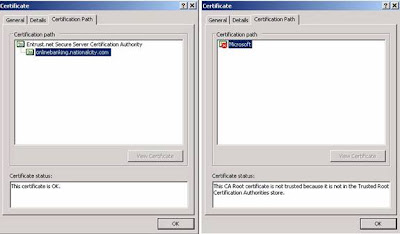 |
| Left One Good Certificate and right one fake certificate |
How an End-User Can Prevent This
- Again, the simple act of viewing the certificate and clicking “No” would have prevented this from happening.
- Education is the key for an end-user. If you see this message, take the time to view the certificate. As you can see from the examples above, you can tell when something doesn’t look right. If you can’t tell, err on the side of caution and call your Online Bank or the Online store.
- Take the time to read and understand all security messages you receive. Don’t just randomly click yes out of convenience.
How a Corporation Can Prevent This
- Educate the end-user on the Security Alert and how to react to it.
- Utilize One Time Passwords, such as RSA Tokens, to prevent the reuse of sniffed credentials.
- When using SSL VPN, utilize mature products with advanced features, such as Juniper’s Secure Application Manager or Network Connect functionality.