Do
you know that each and every computer/laptop having Network Interface
Card (NIC) also known as Ethernet card has a Unique MAC Address?
What is the need and Significance of Unique MAC address?
MAC
address also known as Media Access Control is a 48 bit hexadecimal key
which identifies a machine of Network when connected to LAN/WAN.
The
Unique MAC address is burnt in the ROM of the Ethernet card. Whenever
any request is sent on Network, The ARP packets contain IP address of
the Machine along with the MAC address which uniquely identifies a
Machine on Network.
Let’s take up a scenario to explain the significance of the MAC address
In
today’s world of digitalization, whatever electronic devices you have,
it has connectivity features like Bluetooth or Wi-Fi. Whether it may be
Mobile Phone, IP cameras, Printer/Scanners, PDAs, Laptops, Network HDDs,
etc…
So each and every above such devices should have a unique MAC address.
Consider
the above Image scenarios wherein many devices are connected to a Wi-Fi
router. Whenever you try to connect the Device with router an ARP
(Address resolution Protocol) packets is sent from the device to the
router.
The
ARP packet which is sent from the device contains the MAC address of
its Network Interface controller. As soon as the ARP packets are
received by the router, the router checks for Authentication of the
device and if the device is Authentic then it sends RARP Packet (Reverse
ARP).
RARP
Packet contains the MAC address and the IP which has to be assigned to
the device. Since there can be many devices simultaneously trying to
connect the router, the RARP packet will be broadcasted to all the
devices.
But
only those devices which match with the MAC address of the RARP packet
will be able to accept it and get the Assigned IP address to the device.
Since the packets are broadcasted, if the devices doesn’t have a unique
MAC address it won’t be able to interact with the Layer 3 devices on
Network and Hence will be unreachable from the network.
How MAC address spoofing can result in Hacking and IS breach
Nowadays
everywhere Wi-Fi routers are used to connect to devices like Laptops,
PDA, Mobile Phones, etc… replacing the old CAT5 cable.
In
case of Wi-Fi, since it is an air interface the signals are reachable
to surrounding areas also and thus can be used by any intruder who has
the Wi-Fi signal reachability to enter in to the secured network and
gain access to the important/crucial information thus resulting in
Information security breach.
So
as to avoid this, almost all the Wi-Fi router comes with MAC filtering.
Which means that the network admin of the Router can already specify
that only the listed MAC address are authentic and should be allow to be
connected and rest other devices should be blocked.
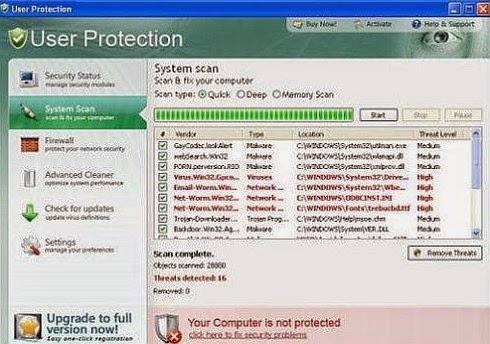
See
below the Screenshot of my Home Router in which I have specified only
two MAC address. So whenever anyone else with other than this mentioned
MAC address is in the range on the network and tries to connect to the
device it will be blocked because the MAC address filtering is enabled.
So
in this case we can spoof the MAC address with the one which is allowed
and can enter in to the network and use the network resources.
Procedure to Spoof the MAC address
There
are many third party applications available, some free and some paid
with which you can easily spoof your MAC address. But I will let you
know how we can use Windows predefined functionality to Spoof the MAC
address.
1) First click on start, then click on run And type “control netconnections” and click ok
2) The
above command will open network connections, in network connections
find your Network Adapter of which you have to change the MAC address.
3) Right click on the Network adapter and click on Properties and you will see a window similar to below
4) Click on Configure button
5) Click on Advanced Tab as highlighted in the above image.
6) After
click on Advanced tab, choose Network Address as in above image and
then on right hand screen enter a Hexadecimal MAC address with which you
want to spoof your present MAC address
7) Once you have entered the MAC address, click on OK and you are done. Yes! Indeed you are done.
You have successfully spoofed your MAC address.
Check the below screenshot which shows the router settings page on which MAC filtering is Enabled.
Only
PC or devices with the below mentioned MAC address will be allowed or
denied as per the option chooses in the Admin settings of the router. In
case your MAC address is blocked by network Admin, then you can spoof
up and change your MAC address to connect and gain access to the Network
resources.
Even
Most of the ISP bind your Login ID and Password to your PC and in any
case you want to access internet on any other PC, other than in which
the MAC Address is binded by ISP, you can use this method to use
internet on other devices as well.
Many
software applications which are licensed to single user single PC, is
binded using MAC address and that can be reused in many PC using MAC
spoofing.
 Google itself providing many useful articles,videos and forums for
webmasters and bloggers. Google needs quality website with quality
SEO(Stay away from blackhats). For doing this job nicely, you have to be
mastered with their tools.
Google itself providing many useful articles,videos and forums for
webmasters and bloggers. Google needs quality website with quality
SEO(Stay away from blackhats). For doing this job nicely, you have to be
mastered with their tools.